Category: spam
-

Direct Send – What It Is, and What It Isn’t
There are a number of posts online panicking about “Direct Send” and how its the worst thing ever. These appear to have started following Microsoft’s publication of an article on how to turn it off – but lots of the articles get the basic principles wrong and therefore provide poor and inaccurate advice. The blog…
-

Blocking onmicrosoft.com Emails in Exchange Online Protection
There is a considerable uptick in emails from the default domain in Microsoft 365 tenants. These emails come from senders @ tenant.onmicrosoft.com and are not your tenant. Microsoft recently announced recipient external sender limits to reduce this, as the default is 10,000 recipients per day, but will get an additional restriction of no more than…
-

More Frequent Quarantine Notifications in Exchange Online Protection
Available from the end of April 2023 there is now an option to increase the notification interval to end users about items in the quarantine. The Microsoft 365 Quarantine is at https://security.microsoft.com/quarantine and though this is a good link to add corporate intranets, its also a useful one for users to remember and bookmark. Up…
-

Improving Exchange Online Email Deliverability Through Third Party Filtering Services – Trusted ARC Sealer
When you receive emails into Exchange Online and you filter the external messages before arrival with a third party filter such as Mimecast, Proofpoint or others, then you can have DMARC failures that result in messages being junked or quarantined in Exchange Online. Trusted ARC Sealer is a feature of Exchange Online to allow you…
-
550 5.1.8 Access denied, bad outbound sender AS(42003)
“Your message couldn’t be delivered because you weren’t recognized as a valid sender. The most common reason for this is that your email address is suspected of sending spam and it’s no longer allowed to send email. Contact your email admin for assistance.” This is an error you get when your anti-spam “outbound” policy restricts…
-
[New] External Email Notification in Exchange Online
This is a new feature released in March 2021 that adds support in Outlook (Mac, OWA, Mobile) for the display of the external status of the sender – note at the time of writing it does not add this feature to Outlook for the PC. This should be used to replace the way this has…
-
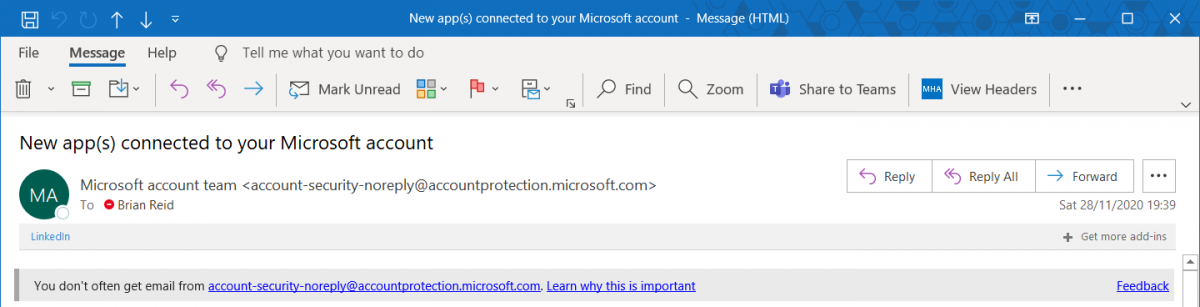
Exchange Online Warning On Receipt Of New Email Sender
Released recently to no fanfare at all, Microsoft now has a SafetyTip that appears if you receive email from a first time recipient. Most often phish emails will come from an address you have never received email from before, and sometimes this email will try to impersonate people you communicate with or are internal to…
-
Enable EOP Enhanced Filtering for Mimecast Users
Enhanced Filtering is a feature of Exchange Online Protection (EOP) that allows EOP to skip back through the hops the messages has been sent through to work out the original sender. Take for example a message from SenderA.com to RecipientB.com where RecipientB.com uses Mimecast (or another cloud security provider). The MX record for RecipientB.com is…
-
Anonymous Emails Between On-Premises and Exchange Online
When you set up Exchange Hybrid, it should configure your Exchange organizations (both on-premises and cloud) to support the fact that an email from a person in one of the organizations should appear as internal to a recipient in the other organization. In Outlook that means you will see “Display Name” at the top of…
-
Enable Report Message Add-In For Office 365
There is a new add-in available for Outlook and OWA in Office 365 that can simplify spam and phishing reporting to Microsoft for content in your mailbox. I recommend rolling this add-in out to everyone in your Office 365 tenant and for Office 365 consultants to add this as part of the default steps in…
-
Get-SpoofMailReport in EOP
Using Office 365 or EOP to protect your email and worried about spoofed emails? Then try this cmdlet in Remote PowerShell for EOP: PS C:\Users\brian.reid> Get-SpoofMailReport Date Event Type Direction Domain Action Spoofed Sender True Sender Sender IP—- ———- ——— —— —— ————– ———– ———14/04/2016 00:00:00 SpoofMail Inbound GoodMail no-reply@domain.com mandrillapp.com 198.2.186.0/2418/04/2016 00:00:00 SpoofMail Inbound …
-
Is Your SenderID/SPF or DKIM Record Correctly Configured
With Microsoft having just announced that DKIM is coming to Office 365 soon (release notes here) and SenderID is already available, I thought this is a good time to write a blog on the use of DMARC to show if your records are correct. DMARC is a protocol that allows you to see the effect…
-
Cannot Send Emails To Office 365 or Exchange Online Protection Using TLS
I have found this is a common issue. You set up an Exchange Online Hybrid or Exchange Online Protection (EOP) stand alone service and follow all the instructions for the creating of the connectors needed, only to find that your emails queue in your Exchange Server. If you turn on protocol logging you get this…
-
Moving Exchange Online Protection Junk Mail to the Junk Email Folder
If you use Exchange Online Protection (EOP) to filter your email in the cloud and to remove spam and malware before onward delivery to you, and if you use Exchange 2007 or later on-premises, then you need to configure Exchange to move detected spam to the Junk Email folder in Outlook. By default EOP detects…