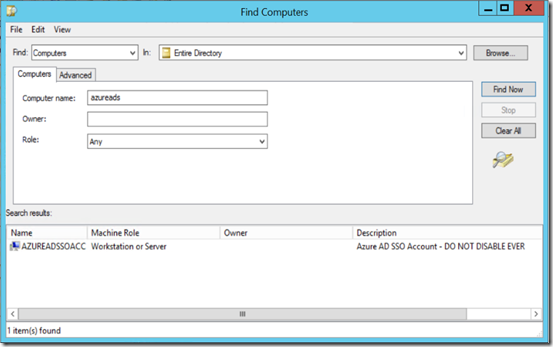
When you set up Azure AD SSO, the Azure AD Connect application creates a computer account called AZUREADSSOACC. Do not disable this account, or SSO stops working.
I’ve had a few clients in the past week disable this when generally disabling all the computer accounts that have not logged in for X days.
Therefore if you have Azure AD SSO enabled, I suggest updating your documentation on disabling computer accounts – ‘cause not all computer accounts actually login as computers (I’m thinking Cluster services here as well) and consider actually whether or not disabling accounts for computers that are not logging in any more is necessary.
Then also take the AZUREADSSOACC account and set a description on it saying do not disable!
Leave a Reply