Announced a few months ago, Advanced Threat Protection became generally available on 1st June. I have been involved with trialling this product during the beta and so I thought I would note down a few thoughts on setting this up and what to expect now that it is publicly available.
Advanced Threat Protection is an add-on product to Exchange Online/Exchange Online Protection with its own subscription, so you will not see these features and products unless you have subscribed. Once you have subscribed you will get two new features in the Exchange Control Panel for Office 365. These are the ability to find malware containing attachments before a detection signature for that malware exists (zero-day malware attacks) and the ability to filter all hyperlinks in email via a known malicious links service (filtering against spear-phishing attacks). The feature to detect zero-day malware is called Safe Attachments and the feature to protect against spear-phishing is known as Safe Links.
Subscribing to Advanced Threat Protection
After signing into the Office 365 administration portal click Purchase Services on the left hand menu and locate your current Office 365 subscription that contains Exchange Online or Exchange Online Protection (Office 365 Enterprise E3 contains EOP, so you would look for your suite purchase if you did not have a standalone purchase of EOP). Your current subscriptions will contain the words Already Purchased underneath the item as shown:
In the two screenshots above you can see that you have no Exchange Online Advanced Threat Protection licences purchased. To add Advanced Threat Protection licences click the Add more link and enter the number of licences you want to purchase. You do not need to purchases the same number of licences as EOP or Exchange Online mailbox licences as you use the policy below to control who Advanced Threat Protection is available for. Advanced Threat Protection for volume licence customers is available from August 2015 and for non-profit/educational licences from later in the year. Once the purchase is confirmed the Advanced Threat’s menu entry appears in the Exchange Administration Console. Also don’t forget to assign a licence to the appropriate users in the Office 365 portal.
Safe Attachments
Safe Attachments in Advanced Threat Protection takes any email that meets the conditions of any one of the Safe Attachment policies that you create that also contains an attachment and checks this email for for malicious behaviour as it passes through Exchange Online Protection (EOP). Before an email is checked by Safe Attachments the attachment has already been scanned for known malware and viruses. So if the attachment contains malware that was not detected by an existing AV signature or if it is a safe attachment (no malware) then the email is routed to the Safe Attachments component in EOP. If the email does not contain any attachments it is routed to the users mailbox by way of the other EOP spam filtering features.
Once an email is considered to have cause to be checked by the Safe Attachments component of ATP the individual attachments in the message are placed inside a newly created Windows virtual machine that is spun up in ATP for the purposes of this service. The attachment is then executed or otherwise run (for example if it is a Word doc, it is opened in Word in the new VM that was created for it). The VM is then watched for behaviour that is considered to be unsafe. Examples of unsafe behaviour include setting certain known registry key locations (such as the RunOnce group of keys in Windows) or downloading malicious content from the internet. If the attachment does not exhibit that behaviour then the email is released and sent on to the user. If the email does exhibit these actions the email is not sent onward, and optionally a copy of the email in a form of a report is forwarded to an administrators mailbox (where care should be taken on opening the attachment).
The time it takes to spin up a new VM and execute the attachment is in the region of 7 to 10 minutes. Therefore anyone subject to a Safe Attachments policy will have emails that contain attachments delayed by at least this amount of time. Of course this delay is necessary to ensure that the recipient is not being sent malware that is currently not detected (zero-day attacks) and the impact of this delay needs to be considered against the benefit of the additional filtering that happens and the impact of that user executing the malware themselves on their own machine.
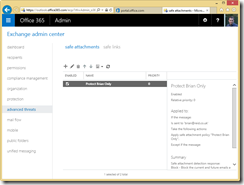
To protect a user with Safe Attachments you need to create a policy. This is done in the Exchange Admin Centre in Office 365 and the “advanced threats” area as shown:
In the above screenshot I have a single policy created called “Protect Brian Only”. This would be an example where I wanted to protect those users whom I though where more likely to be subject to zero-day malware attacks – good examples would be highly targets accounts (CEO etc.), IT administrator/help desk accounts and of course the accounts of users who will click anything and so you are often cleaning up their PC! There is no default policy, so unless a user is protected by a policy that you the administrator create, they are not subject to the Safe Attachments feature.
As Advanced Threat Protection is an additional licence, only those users who are licenced should be included in any policy.
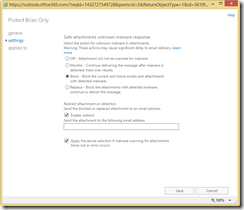
Opening the “Protect Brian Only” example policy above shows me three sets of options. These are:
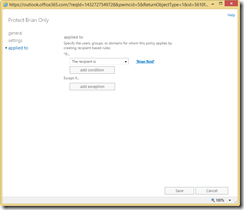
The first page allows me to edit the name and description. The second page sets the policy (more on this below) and the final page sets who the policy applies to. In this example it applies to a single recipient who was selected from the list of users in Office 365, though it could be a list of more than one user or anyone with a given email domain or anyone in an already created group.
The policy setting allows me to do the following:
- Scan attachment containing emails (with options to not do this scanning, scan and send onward to the user regardless of the result, block the emails containing bad attachments or replace the attachments with a notification but allow the contents of the email to go on through).
- Redirect the attachment containing emails to an alternative email address and what address to use. This is great for seeing what is blocked and acting as a sort of reporting service. Warning – this email address will get malicious emails sent to it, handle with extreme care.
- Finally, in the event of a timeout at EOP/ATP where the attachment cannot be scanned in 30 minutes, check this box to treat the attachment in the same way as malicious emails are treated. This is the default action.
In the mailbox of the intended recipient, if block or replace is selected in the policy then the user will not see the malicious attachment and therefore cannot accidently execute its contents.
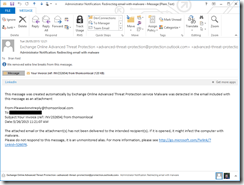
In the mailbox of the email address used for the redirection, you will see messages such as follows:
Here you see a report email that contains the email that was detected as malicious. You can see the To: address (redacted in the graphic above) and that it was not sent to the intended recipient and that it should not be opened.
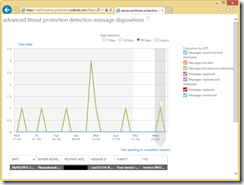
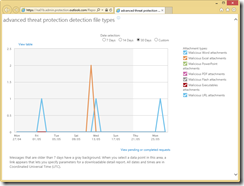
All in all, its a very simple and inexpensive way to protect the mailboxes of either all staff or those you consider subject to targeted malware such as CEO type staff and the IT department. Even if you do not redirect emails containing malicious attachments, you can report on the number and type of attachments that are blocked from the reporting console available from the ![]() icon on the ATP toolbar. The following shows a 30 day report for my tenant (which has only a few live mailboxes protected). For data-points beyond 7 days old it will take a short while for the information on the report to be returned to you and you need to request that report from the provided link. For data-points under 7 days you can see the information in real-time. The grey background to report shows where the 7 day period is located. In the below screenshot the above malware can be see in the report as the single instance of an email that passed AV scanning successfully but was in fact a zero-day attack. The second screenshot below shows the type of malware attachments that ATP is blocking. From this we can see that the risk lies in maliciously crafted Excel and Word attachments.
icon on the ATP toolbar. The following shows a 30 day report for my tenant (which has only a few live mailboxes protected). For data-points beyond 7 days old it will take a short while for the information on the report to be returned to you and you need to request that report from the provided link. For data-points under 7 days you can see the information in real-time. The grey background to report shows where the 7 day period is located. In the below screenshot the above malware can be see in the report as the single instance of an email that passed AV scanning successfully but was in fact a zero-day attack. The second screenshot below shows the type of malware attachments that ATP is blocking. From this we can see that the risk lies in maliciously crafted Excel and Word attachments.
Safe Links
When an email is delivered to the end recipient, any technology that checks the target of any link in the email is prone to one large issue – the web page or attachment on the other side of the hyperlink in the email may be safe and okay to view at the time of delivery, but might not be at the time the user comes to open the email and then click the link. Being aware of users working, or at least email reading hours, and delivering emails outside this timeframe with links to websites that are okay at the time of delivery means the email passes any web site or download checks done by the email server.
Advanced Threat Protection’s Safe Links feature protects the user by rewriting the hyperlink in the email body so that the link is checked at the point of click and not the point of delivery. To do this the hyperlink is changed from the target to the Safe Links portal. Then when the user clicks the link, they are taken to the Safe Links portal and if the site is now on a block list, the user is blocked, but if the target of the link is fine they are sent a browser redirect to the original target. Note that this is not a proxy server – you do not connect to the target URL through the Safe Links portal, you just visit the Safe Links portal when you click the link and if the target is safe at point of click you are directed via your browser to the target (a client side redirect). If the target is not safe at point of click then an error page is displayed.
In the following screenshot is an email with a hyperlink in it. This link was received by me to my Safe Links protected account and it looks link it might be an attempt to download malware to my computer, but I am going to click the link anyway (in second screenshot I am hovering over the hyperlink):
You can see from the above screenshot that the hyperlink takes the user first to https://na01.safelinks.protection.outlook.com/?url=targetURL&data=value&sData=otherValue. The na01 part of the URL will be regionally specific and so might read emea01 or apac01 etc. When the user clicks the link they go to region.safelinks.protection.outlook.com. In my case I see the following webpage:
Here I am told the page has been classified as malicious. I also have an option to continue anyway (and I can control if this setting appears for users or not) and an option to close the browser window.
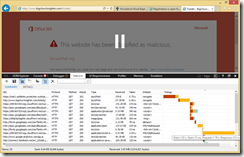
If the hyperlink is not malicious at the point of click then I still go to the Safe Links portal (as it is the portal that checks the link at point of click), but then get redirected to the target URL. This can be seen in the following screenshot which shows the F12 developer tools enabled in the browser and the network trace screen shown at the bottom of the window:
You will see that the first line is the Safe Links portal and this take 0.75 second before being redirected with a HTTP 302 client side redirect to the target URL and then the rest of the objects on the target page (until I paused the trace).
So how do I set this all up? It is very similar to the Safe Attachments above in that we create a policy, and then any email that contains hyperlinks that is delivered to the end user after that users is added to a policy get rewritten.
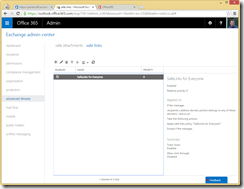
First we go to the Advanced Threats area of the Exchange Administration Console:
Here you can see an existing policy. There are no policies by default. If I create a new policy I need to provide the following:
You can see from the screenshot that you need a name for the policy and whether or not a link is rewritten (policies with greater priority take precedence, so if a user is subject to two or more polices then only the higher priority policy takes effect, therefore you can use a policy to turn off link rewriting for a subset of users covered under a lower policy that enabled it for more users). Also you can disable link tracking and not to allow users to have the option to click through to the target URL. Link tracking allows you to report who clicked what link and not allowing users to click through disables the “Continue to this website (not recommended)” link on the Safe Links warning page.
You also have the ability to control URL’s that you do not want to rewrite, and rewriting will only happen for FQDN URL’s (that is those with dots in them) and not single name URL’s such as http://intranet. This allows you to bypass redirection for sites you know are safe or are FQDN’s but are internal.
Finally you get to set who the policy applies to. You do not need to apply the policy to all users if you have not licenced all users, but you can set policy based on who the recipient is, what domain the recipient is in (all users in that domain) or a group (some users).
On the Mail Flow menu in Exchange Control Panel you can view a URL Trace of the links that users have clicked in the past 7 days. The report shows you the link clicked and if it was blocked or not. If the click through option is enabled, it will show if that was done as well. Only users in policies that track clicks will be reported. As report looks like the following:
Further Administration
To administer your Safe Links and Safe Attachments policy and rules via Remote PowerShell see http://c7solutions.com/2015/06/advanced-threat-protection-via-powershell





Leave a Reply