Category: self-service password reset
-

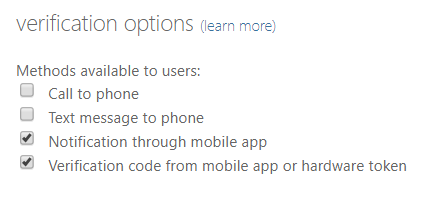
Migrating MFA Settings To Authentication Methods
Released to Azure AD in December 2022 there is now a process for migrating from the legacy MFA methods and Self-Service Password Reset (SSPR) authentication methods to the unified Authentication Methods policies in Azure AD. This migration window is open until September 2025 (originally January 2024) when the legacy methods will be disabled. This change…
-
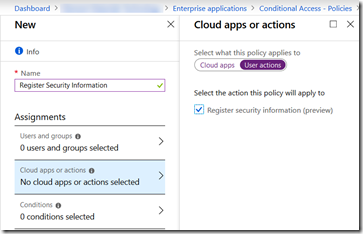
Register For Azure AD MFA From On-Premises Or Known Networks Only
A long request within Azure AD/Office 365 has been the request to be able to register your security info from a known location or only on certain other conditions. Well it looks like this has appeared in Azure AD in the last few days!! Its visible under Azure AD > Conditional Access > New/Existing Policy…