Category: token2
-
Hardware Tokens for Office 365 and Azure AD Services Without Azure AD P1 Licences
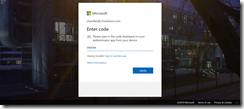
A recent update to Azure AD Premium 1 (P1) licence has been the use of hardware tokens for multi-factor authentication (MFA). This is excellent news if your MFA deployment is stuck because users cannot use phones on the shop floor or work environment or they do not want to use personal devices for work activities.…
-
Token2 Hardware OAuth Tokens and Azure AD Access
This blog post walks through the process of logging into Azure AD resources (Office 365, other SaaS applications registered in Azure AD and on-premises applications that utilise Azure AD App Proxy). First step is to order your desired hardware. For this article we are looking at the devices manufactured by Token2 (www.token2.com). These include credit…